Disposable emails are temporary, anonymous email addresses designed for short-term use. They work by generating a random inbox that automatically deletes itself after a set time or use limit, shielding your primary email from spam, data breaches, and unwanted tracking. These services are perfect for signing up to websites, downloading files, or verifying accounts where you don’t want to share your real contact information. They provide a simple, effective layer of digital privacy for everyday online interactions.
You’re about to download a fantastic, free e-book that promises to revolutionize your workflow. The landing page looks professional, the author is credible, and you really want the content. There’s just one tiny, frustrating hurdle: a form demanding your email address. You hesitate. Your primary inbox is already a chaotic battlefield of promotional blasts, newsletter overload, and the occasional phishing attempt. What if this is just another tactic to flood your space with unwanted mail? What if your email gets sold to a third-party list you never heard of? This is the universal modern dilemma: the cost of “free” is often your contact information. But what if you could say “yes” to the download and “no” to the spam? Enter the world of disposable email—a simple, powerful tool for reclaiming your digital privacy. This guide will unpack exactly how these temporary inboxes function, why they’re so effective, and how you can use them wisely.
Think of a disposable email service as a digital burner phone. Just as you might get a cheap, prepaid phone for a temporary need and then discard it, a disposable email gives you a throwaway address for a specific online interaction. It’s not meant for long-term correspondence or accessing critical services. Its sole purpose is to act as a shield, intercepting the digital debris that comes with participating in the modern web. The magic lies in its simplicity and its automatic cleanup. You don’t have to remember to delete anything; the system handles the sanitization for you. In the following sections, we’ll peel back the layers on this technology, from the moment you request an address to the second it vanishes into the digital ether.
Key Takeaways
- Core Concept: A disposable email is a temporary, randomly generated inbox that self-destructs after a short period (e.g., 10 minutes to 24 hours) or a limited number of messages.
- Mechanism: You visit a temp mail site, get a random address, use it publicly, and check the inbox on the provider’s site. No password or personal info is typically required.
- Primary Benefit: It creates a protective barrier, preventing spam, marketing emails, and potential data leaks from reaching your permanent, personal email account.
- Ideal Use Cases: Signing up for newsletters, forum registrations, downloading gated content (e-books, whitepapers), and verifying accounts for non-critical services.
- Key Limitation: They are not for important accounts (banking, social media, primary cloud storage) as the inbox and its contents vanish permanently.
- Privacy Trade-off: While they hide your real email, the disposable provider *can* see any emails sent to that temporary address, so don’t use them for highly sensitive information.
- Best Practice: Use a reputable provider, never use them for password recovery on important accounts, and assume any data entered while using the temp email could be linked to that temporary address.
📑 Table of Contents
- What Exactly Is a Disposable Email?
- The Step-by-Step Mechanics: From Click to Cleanup
- Core Benefits: Why Use a Disposable Email?
- Common Use Cases: When to Reach for a Temp Mail
- Critical Limitations and Risks: What Disposable Emails Can’t Do
- Best Practices for Safe and Effective Use
- The Future of Temporary Inboxes and Digital Privacy
- Conclusion: A Simple Tool for a Complex Problem
What Exactly Is a Disposable Email?
At its heart, a disposable email (also called a temp mail, throwaway email, or fake email) is a service that provides users with a temporary email address and associated inbox. The defining characteristics are anonymity and ephemeral nature. Unlike creating an account with Gmail, Outlook, or ProtonMail, you typically do not need to provide any personally identifiable information to get a disposable address. The email address itself is usually a long, random string of characters (like a7b9c3@domain.temp) generated by the service’s system.
The “disposable” part is enforced automatically. These inboxes have a built-in expiration timer. Some services delete the inbox after 10 minutes of inactivity, others after 1 hour, and some offer a 24-hour window. Many will also destroy the inbox once it receives a certain number of messages (e.g., after 3 emails). Once the timer hits zero or the message limit is reached, the address and all its contents are permanently purged from the server. Attempting to access it later will result in a “not found” or “expired” message. This design philosophy ensures the address can’t be reused to target you later and that your temporary digital footprint is wiped clean.
The Architecture of Anonymity
The technical setup behind a disposable email service is surprisingly straightforward, which is part of why so many free providers exist. It relies on a few key components working in tandem:
- Random Address Generator: The core engine creates unique email addresses on the fly. It combines random strings (letters, numbers) with the service’s domain name (e.g., @tempmail.demo, @10minutemail.com).
- Catch-All Mail Server: The service’s mail server is configured to accept emails sent to *any* address at its domain. It doesn’t need to pre-create individual mailboxes. When an email arrives for xyz123@service.com, the server catches it.
- Inbox Mapping Database: A temporary database links the randomly generated address (like xyz123) to the specific browser session or IP address that requested it. This is how the service knows which inbox to show you when you revisit the site.
- Automatic Purge System: A cron job (scheduled task) constantly scans the database for expired inboxes based on time or message count and deletes their entries and associated emails from the server.
Because no account is created, there’s no password reset, no profile, and no stored user data linking the address back to you personally. The connection exists only in your current browser session, often stored in a temporary cookie or local storage.
The Step-by-Step Mechanics: From Click to Cleanup
Understanding the user journey clarifies the entire process. Let’s walk through a typical scenario where you use a disposable email to sign up for a webinar.

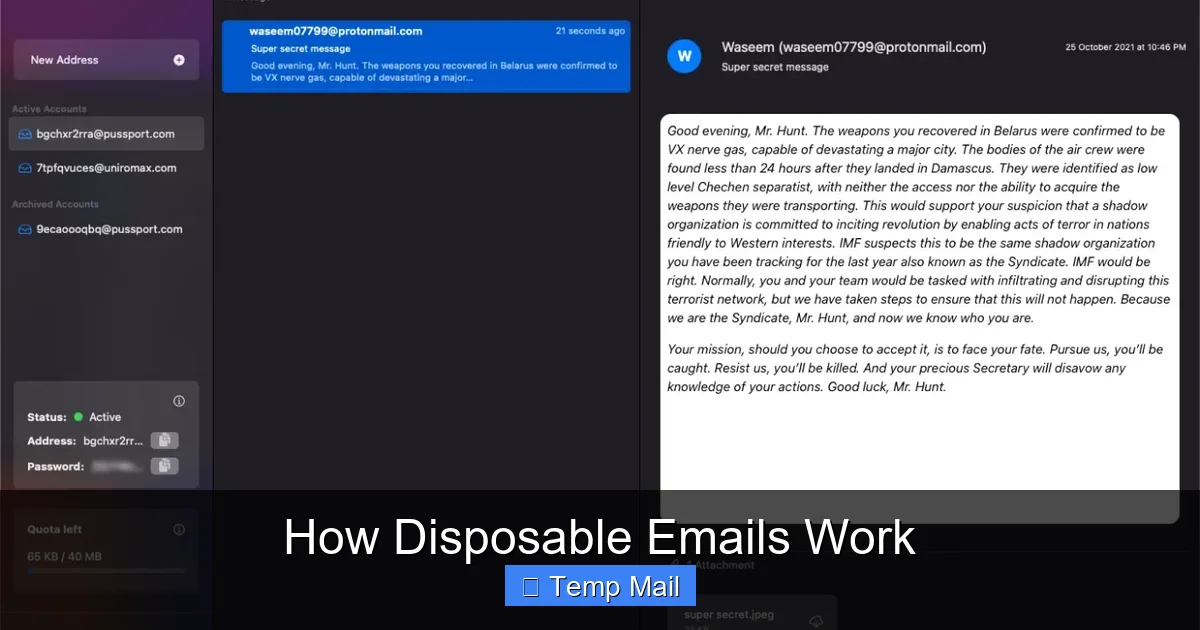
Visual guide about How Disposable Emails Work
Image source: funkyspacemonkey.com
Step 1: Generation & Assignment
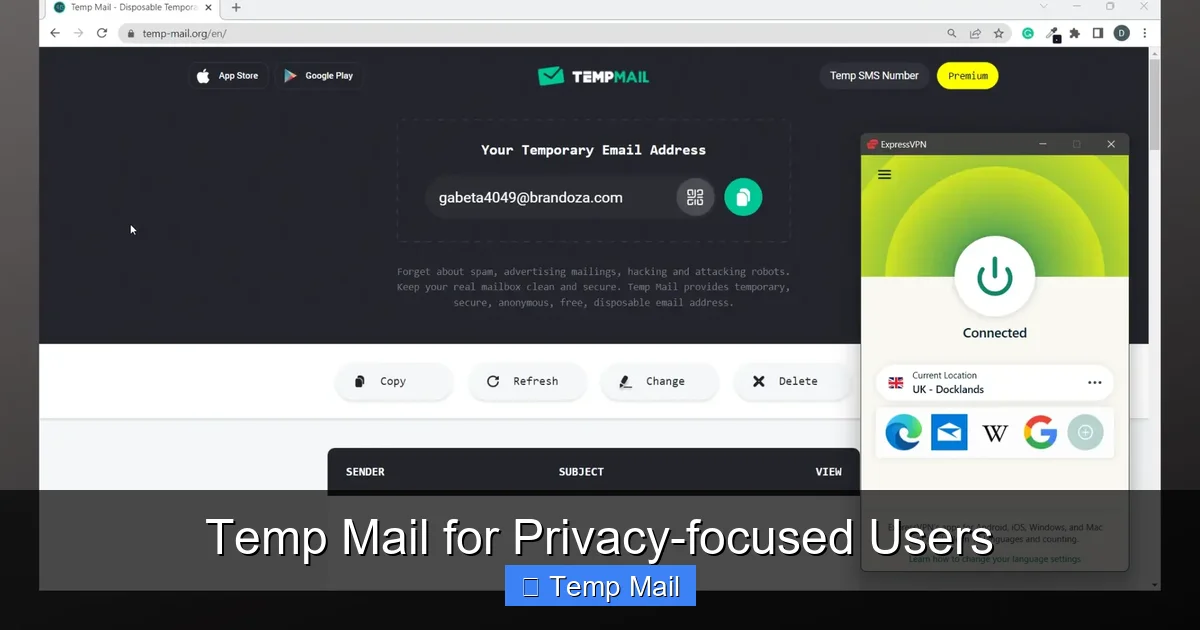
You navigate to a site like Temp-Mail.org. The moment the page loads, the backend system springs into action. It generates a completely random email address, for example, w7k4p2@temp-mail.io. It then creates a unique session identifier and stores this pair (the address and the session ID) in its temporary database, along with a timestamp. This entire process takes milliseconds. The newly minted address is displayed prominently on your screen. You copy it.
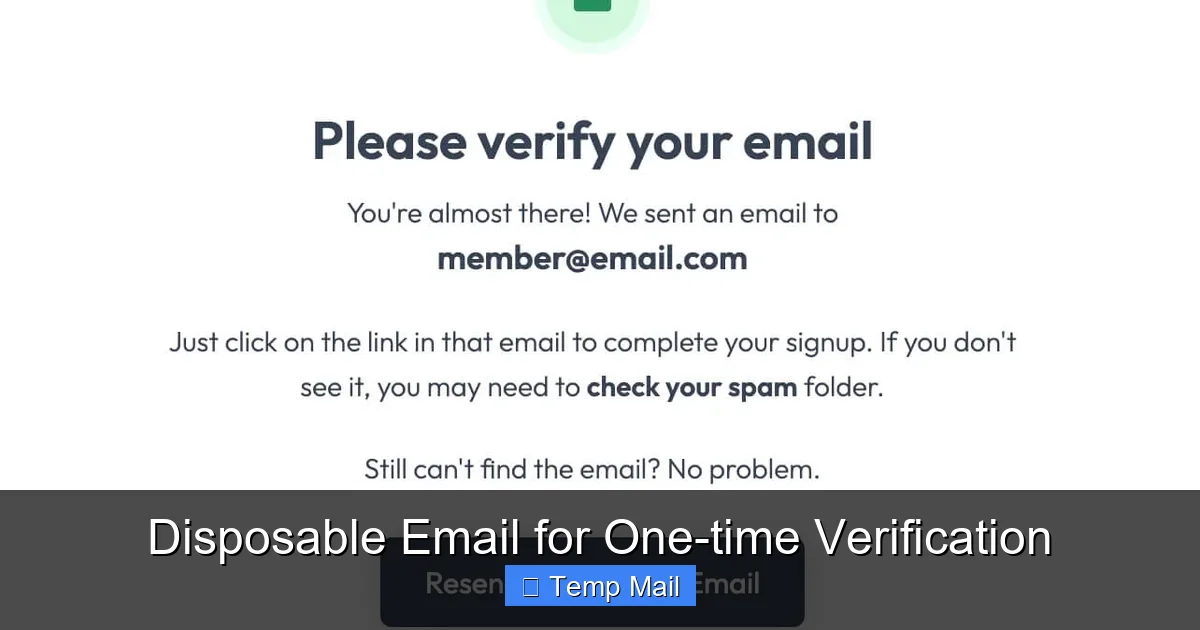
Step 2: Public Use
You paste w7k4p2@temp-mail.io into the webinar registration form and submit it. The webinar platform sends a confirmation email to that address. That email travels through the standard internet mail routes and lands in the catch-all server of temp-mail.io. The server receives it, sees the recipient is w7k4p2, looks up the corresponding session in its database, and deposits the email into that specific inbox queue.
Step 3: Retrieval
You switch back to your temp mail browser tab (or refresh it). The site reads your session cookie, queries its database for the address linked to your session, and fetches all emails waiting in that inbox. The confirmation email from the webinar platform appears in your list. You can open it, read it, and click any links within it—all within the confines of the temp mail provider’s interface. The webinar platform has no idea you’re using a disposable address; from its perspective, it sent an email to a valid, active mailbox.
Step 4: Automatic Expiration & Purge
The clock is ticking. The temp mail service’s system noted the creation time of w7k4p2. If the service has a 1-hour policy, 60 minutes after generation, a scheduled cleanup task will find this address in the database. It will delete the database entry and all stored email data for w7k4p2 from the mail server. The address is now gone forever. If you try to access the inbox later, the service won’t find the session and will generate a *new* random address for you. The webinar’s confirmation email, and the fact you ever used that address, is erased from the service’s side.
This entire lifecycle is automated, requires zero user maintenance, and leaves no persistent credentials behind. It’s privacy through transience.
Core Benefits: Why Use a Disposable Email?
The appeal of disposable emails isn’t just about avoiding a cluttered inbox; it’s a fundamental tool for digital hygiene and security. The benefits cascade from that single act of separating your primary identity from low-stakes online activities.
Visual guide about How Disposable Emails Work
Image source: funkyspacemonkey.com
1. Spam and Junk Email Mitigation
This is the most obvious and valuable benefit. When you use your permanent email for every free download, forum sign-up, or contest entry, you are effectively handing out your digital home address to anyone who asks. Many websites, even reputable ones, have weak data security or share email lists with advertising partners. Your address gets sold, traded, and harvested. Disposable emails intercept this flood. All the promotional newsletters, “special offers,” and unsolicited emails get sent to the temporary address, which self-destructs before the spam can even reach your primary inbox. Your important, personal, and work emails remain pristine and easy to manage.
2. Enhanced Privacy and Anonymity
Every website you register with collects data. Your email address is a primary key that can link your activity across different sites, building a profile of your interests, location (via IP logs), and behavior. Using a disposable email breaks this link chain. It’s much harder for a data broker to connect your activity on Site A (using temp mail) with your activity on Site B (using a different temp mail) or your real identity. It provides a layer of anonymity for browsing, research, or any activity where you don’t want to establish a persistent online identity.
3. Protection from Data Breaches
Data breaches are a matter of “when,” not “if.” When a company you signed up with suffers a breach, hackers often steal user databases, which include email addresses. These breached email lists are then used for phishing attacks, credential stuffing (trying common passwords on other sites), or sold on the dark web. If you used a disposable email for that breached service, the compromised address is already expired and useless to attackers. Your precious, permanent email—and the other accounts linked to it—remain safe from that particular breach’s fallout.
4. Simplified Testing and Development
For software testers, developers, and QA professionals, disposable emails are indispensable. They need to test email verification flows, password reset mechanisms, and notification systems. Creating hundreds of real email accounts is impractical. Temp mail services allow testers to generate a new, unique inbox for each test case, verify the system sends the correct email, and then discard the address. It streamlines the entire testing lifecycle.
5. Bypassing Unnecessary Gatekeeping
Many websites gate valuable content (research papers, software trials, design templates) behind an email form. Often, the content is freely available elsewhere or the site just wants to build its mailing list. Using a disposable email allows you to access the resource you need without committing to a long-term marketing relationship you don’t want. It’s a way to politely say “I’ll take the content, but not the newsletter” to websites that force the two to be linked.
Common Use Cases: When to Reach for a Temp Mail
Knowing the benefits is one thing; knowing exactly when to use them is the key to effective practice. Here are the most common and appropriate scenarios.
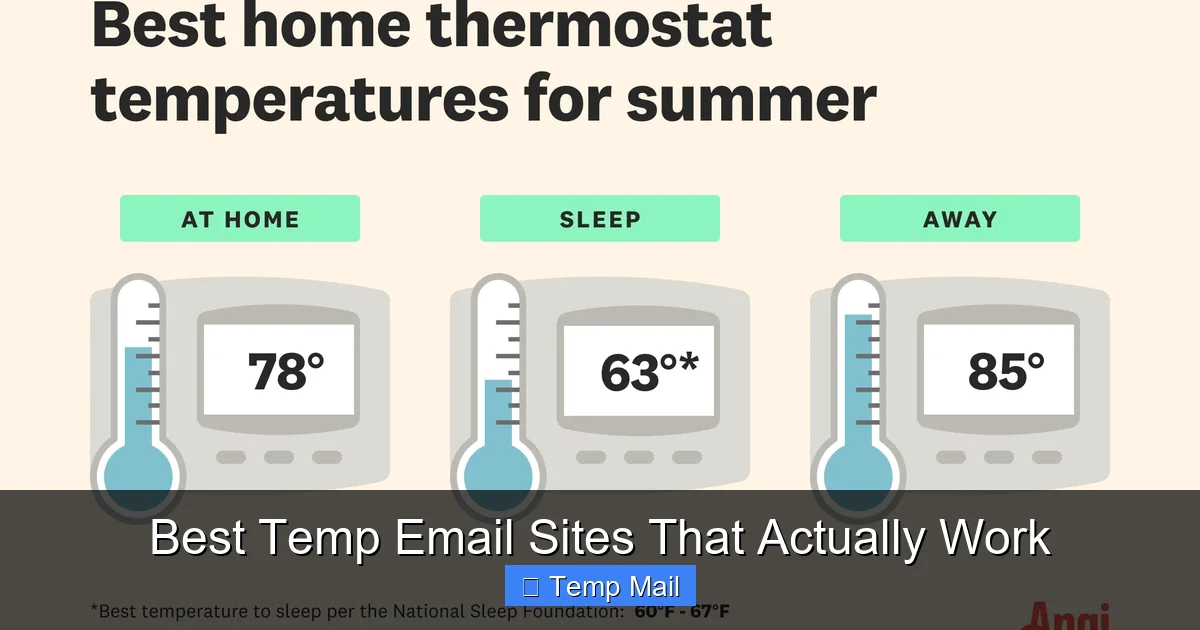
Accessing Gated Content
This is the #1 use case. You want an e-book, a webinar recording, a industry report, or a software trial. The form asks for an email. Use a disposable address. You get the download link, and you never hear from them again (because the address expires). It’s a clean, one-time transaction.
Registering for One-Time Events or Forums
Signing up for a single online event, a workshop, or a community forum you might only visit once? Use temp mail. You get the registration confirmation and any event details, but you won’t be subjected to a lifetime of forum digest emails or event promotions for similar, future webinars you have no interest in.
Testing Online Services
Want to try a new SaaS tool’s free tier without the sales team immediately calling you? Use a disposable email for the trial sign-up. You can test the product’s core features without your contact info entering their CRM pipeline. Similarly, if you’re testing an app that requires email verification, a temp inbox is perfect.
Downloading from Less-Trusted Sources
You’re on a blog or file-sharing site you’re unfamiliar with. It promises a useful plugin or template, but the site’s design is questionable, and you suspect the primary goal is harvesting emails. A disposable email lets you proceed cautiously. If the download link is legitimate, you get your file. If the site immediately starts spamming the inbox, you know to avoid it—and the inbox will die soon anyway.
Creating Accounts for “Burner” Purposes
Sometimes you need an account for a very specific, temporary purpose. Examples include: a social media account to follow a single event or trend, a gaming account to try a game before committing, or a profile on a classifieds site to make a single post. A disposable email facilitates this without tying the activity to your main identity.
Critical Limitations and Risks: What Disposable Emails Can’t Do
Disposable emails are powerful, but they are not a magic bullet for all privacy concerns. Understanding their limitations is crucial to using them safely and effectively. Misusing them can lead to real problems.
1. Not for Important, Long-Term Accounts
This is the golden rule. Never, ever use a disposable email for any service where account recovery is critical. This includes:
- Banking, financial services (PayPal, Venmo, crypto exchanges)
- Primary email accounts (Gmail, Outlook, iCloud)
- Cloud storage (Dropbox, Google Drive, iCloud)
- Social media profiles you want to keep (Facebook, Twitter, Instagram, LinkedIn)
- Any subscription service with recurring billing (Netflix, Spotify, software licenses)
- Government or healthcare portals
Why? If you forget your password or need to reset it, the recovery email will be the disposable address—which is already gone. You will be permanently locked out of the account, often with no way to recover it. You could lose money, data, or access to essential services.
2. The Provider Sees Your Emails
While the *website you signed up with* doesn’t know your real email, the disposable email provider has full access to all emails sent to that temporary address. You are placing trust in that provider not to log, read, or misuse the content of those emails. For casual sign-ups and newsletters, this risk is minimal. But you should never use a disposable email to receive:
- Password reset links for important accounts (see above).
- Medical records, financial statements, or legal documents.
- Any communication containing highly sensitive personal data (SSN, credit card numbers, confidential contracts).
- Private communications you expect to be encrypted end-to-end.
Assume anything sent to a temp mail inbox could be read by the service provider.
3. Many Sites Actively Block Them
Disposable email domains are well-known. Many websites, especially those dealing with finance, security, or high-value transactions, maintain real-time blocklists of known temp mail domains. They check the domain part of the email address during registration. If it matches a blocklist (e.g., @mailinator.com, @10minutemail.com), the sign-up is rejected. You’ll get an error like “Please use a valid corporate or personal email address.” This is a security measure for them, but it can be a hurdle for legitimate, low-stakes use. You may need to try a less common temp mail provider if your first choice is blocked.
4. No Persistent Storage or Search
The inbox is temporary. If you receive an email with a crucial link or code and accidentally close the tab before copying it, that information is likely lost forever once the session expires or the inbox purges. There is no “search your archive” because there is no archive. You must be attentive and extract any needed information immediately upon receipt.
5. Potential for Abuse and Blacklisting
Because they are anonymous, disposable emails are frequently used for malicious purposes: creating spam accounts, signing up for services with fake identities, or bypassing bans. As a result, emails sent from some disposable domains can have poor sender reputation. If a website you’re trying to register with uses email verification, their system might flag the confirmation email as spam or reject it outright because it originates from a known “disposable” domain. While this usually affects the *sending* side (the website sending *to* you), it can occasionally cause delivery issues.
Best Practices for Safe and Effective Use
To get the most out of disposable emails while avoiding pitfalls, follow these practical guidelines.
Choose Your Provider Wisely
Not all temp mail services are created equal. Look for these features:
- No Registration Required: The best ones work instantly from the homepage.
- Clear Expiration Policy: The site should state clearly how long inboxes last (e.g., “Emails are stored for 1 hour”).
- HTTPS Encryption: Ensure the site uses HTTPS to protect the session and the emails you view from eavesdropping.
- Domain Variety: Some providers offer multiple domain choices (e.g., @tmpmail.org, @tmpmail.net). If one domain is blocked on a site, try another.
- Ad Load: Free providers are ad-supported. Expect pop-ups and banners. Be careful not to click misleading ads that look like “download” or “continue” buttons. A reputable provider will have clear ad placements.
Do a quick search for “best disposable email 2024” to see current community recommendations, as provider popularity and reliability can change.
Use a Dedicated Browser or Profile
For an extra layer of separation, use a different browser (e.g., Firefox if you normally use Chrome) or a dedicated browser profile/incognito window for your disposable email activities. This prevents any cookies or local storage from your temp mail session from mixing with your main browsing data. It’s a simple step that reinforces the “burner” concept.
Never Mix and Match
Do not use a disposable email to sign up for a service and then later try to log in with it using your main browser where you’re logged into personal accounts. The session might not carry over. If you need to access a service again, realize the disposable address may have expired. For any service you might return to, use your real email from the start, or accept that you may lose access when the temp address dies.
Extract and Securely Store Critical Info Immediately
As soon as you get a confirmation email with a link, a discount code, or a license key, copy it and paste it into a secure note (like a password manager or an encrypted document) before doing anything else. Do not rely on the temporary inbox to remain accessible for later reference. Treat the inbox as a real-time message stream, not storage.
Know When to Abandon Ship
If a website demands more verification than you’re comfortable with even with a temp email (e.g., phone number, ID scan), it’s a sign the service may not be appropriate for a disposable address strategy, or it may simply be too high-value for your needs. It’s okay to walk away. The goal is low-friction access, not jumping through hoops.
Use Them Proactively, Not Reactively
The best time to use a disposable email is before you enter your primary address on a form. Make it your default reflex for any non-essential sign-up. Don’t wait until after you’ve already received spam to your main account; prevention is the entire point.
The Future of Temporary Inboxes and Digital Privacy
The disposable email exists because of a fundamental imbalance in the digital economy: personal data, especially email addresses, is treated as a commodity. As privacy regulations like GDPR and CCPA have given users more rights, the pressure on companies to be transparent about data use has increased. However, the practice of email harvesting for marketing remains pervasive. This ensures that tools like disposable emails will remain relevant.
We are also seeing evolution in the space. Some providers now offer slightly longer-term “alias” features (like Apple’s “Hide My Email” or Firefox’s “Relay” service) that create unique, forwardable addresses that can be disabled on demand. These are more integrated and user-friendly but often tied to a paid ecosystem. Truly anonymous, no-strings-attached disposable emails will likely always have a place for quick, anonymous, one-off interactions where even an alias service feels like overkill.
The broader trend is toward privacy-by-default. As user awareness grows, we may see more browsers and operating systems building in temporary communication tools. The concept of a “digital shadow” is becoming widely understood, and disposable emails are a simple, effective first line of defense for anyone looking to shrink that shadow. They democratize privacy, requiring no technical skill and costing nothing.
Conclusion: A Simple Tool for a Complex Problem
Disposable emails work on a beautifully simple premise: create a digital address, let it receive messages for a short time, then erase all traces. This mechanism directly counters the modern web’s tendency to treat your primary email as a permanent, monetizable identifier. They are not a tool for secrecy in clandestine activities, but rather a mundane yet powerful instrument for intentional living in the digital age. They allow you to participate in the web’s offerings—its free content, its trials, its communities—without surrendering your core communication channel to the noise.
By understanding their mechanics, respecting their limitations, and applying the best practices outlined here, you can seamlessly integrate disposable emails into your digital routine. Use them for the gated e-book, the one-off forum, the trial software. Keep your permanent email for your bank, your family, your real friends, and the services you truly trust. In doing so, you take back control. You transform your primary inbox from a spam-ridden wasteland back into a functional, trusted space. That’s not just convenience; that’s a fundamental act of digital self-care. The next time a website asks for your email, you’ll have a clear, confident answer—and a temporary address ready to give.
Frequently Asked Questions
Are disposable emails legal to use?
Yes, using disposable email services is perfectly legal in most jurisdictions. They are a legitimate privacy tool. However, using them to commit fraud, evade legal obligations, or send malicious content is illegal. The tool itself is neutral; it’s the intent behind its use that determines legality.
Are disposable emails secure?
Security is relative. For basic privacy from spam, they are effective. The connection to the temp mail site is usually HTTPS-encrypted. However, the provider can see all emails sent to your temporary address, and the inboxes lack the robust security (like 2FA, encryption at rest) of major providers. Do not use them for sensitive data or account recovery.
How long do disposable emails last?
It varies by provider. Common expiration times are 10 minutes, 1 hour, 1 day, or until a certain number of messages (e.g., 3) are received. Always check the specific service’s policy. Once expired, the address and all its emails are permanently deleted from the server.
Can I send emails from a disposable address?
Most disposable email services are designed for receiving emails only. They typically do not have SMTP servers configured to allow you to send outgoing mail from the temporary address. Their primary function is to receive verification links and notifications from websites you register with.
What happens if a website I signed up with emails me important info later?
That information will be lost. Since the disposable inbox has expired, the email will bounce or be discarded. This is why the cardinal rule is to never use a disposable email for any account where future communication is important, such as password resets, billing statements, or service updates.
Are there any free, reliable disposable email services?
Yes, there are many reputable free providers. Popular and generally reliable options include Temp-Mail.org, 10MinuteMail.com, and Guerrilla Mail. Their longevity depends on staying off spam blocklists, which can change. If one is blocked on a site you’re trying to register with, try another provider or a different domain from the same service.