Tired of your personal email getting bombarded with spam after every online sign-up? A temporary email service provides a disposable, secure address you can use for registrations, downloads, or any site you don’t fully trust. It’s a simple, free tool that acts as a protective shield, keeping your primary inbox clean and your digital footprint private. By using a throwaway address, you take control of your online privacy and significantly reduce the risk of your main email being sold, hacked, or flooded with marketing clutter.
Key Takeaways
- Primary Defense Against Spam: Temporary emails intercept promotional and unsolicited emails, keeping your permanent inbox clutter-free and organized.
- Enhanced Privacy Protection: They prevent websites from linking your real identity and primary email to your browsing and registration activities.
- Mitigate Data Breach Risks: If a site using your temporary email is breached, hackers only get access to an expired, inactive address, not your core credentials.
- No Long-Term Commitment: These addresses are designed for single-use or short-term tasks and auto-delete, requiring no management or manual cleanup on your part.
- Simple and Instant Access: Generating a new disposable email address takes seconds, with no registration or personal information required from you.
- Not for Critical Accounts: They are ideal for one-time sign-ups and low-stakes interactions but should never be used for banking, primary social media, or essential services where account recovery is vital.
- Tool for Digital Hygiene: Regular use is a proactive habit for managing your digital identity and controlling which entities have access to your primary contact point.
📑 Table of Contents
- Introduction to Temporary Email: Your Digital Bodyguard
- The Problem with Using Your Personal Email Everywhere
- How Temporary Email Services Work: Simplicity Itself
- Choosing the Right Temporary Email Provider
- Best Practices for Secure Registrations with Temp Mail
- The Future of Digital Privacy and the Role of Disposable Addresses
- Conclusion: Reclaim Your Inbox and Your Privacy
Introduction to Temporary Email: Your Digital Bodyguard
Imagine you’re at a crowded, noisy party. Someone you barely know asks for your home address. You wouldn’t hand it over, right? You might give a P.O. box or just say no. In the digital world, your primary email address is that home address. Every time you sign up for a new online service, download an e-book, or enter a contest, you’re often asked to provide it. Many of us comply without a second thought, not realizing we’re handing over a key to our digital lives. This is where the humble, powerful temporary email service becomes your essential ally for secure online registrations.
A temporary email, also called a disposable or throwaway email, is a service that provides you with a random, functional email address for a short period—usually 10 minutes to a few hours. You can use it to receive a single verification link or download file, and then it vanishes into the ether. It’s not meant for long-term communication. Its sole purpose is to act as a shield, absorbing the spam, potential data leaks, and tracking cookies that would otherwise target your permanent inbox. In an era of rampant data harvesting and constant cyber threats, using a temporary email for non-critical sign-ups isn’t just clever; it’s a fundamental practice in modern digital hygiene and security.
The Problem with Using Your Personal Email Everywhere
So why is using your main Gmail, Outlook, or Yahoo address for every random website such a bad idea? The problems are both an annoyance and a genuine security risk. Let’s break down the cascade of issues that stem from this common habit.
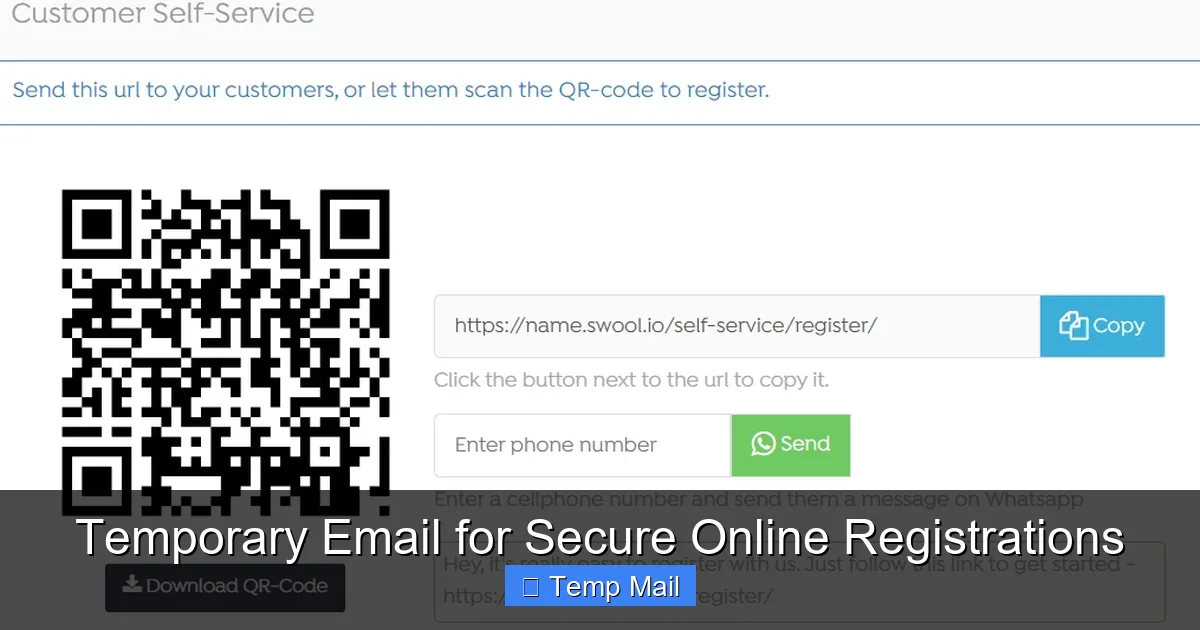
Visual guide about Temporary Email for Secure Online Registrations
Image source: swool.io
The Spam Avalanche
The most immediate and visible consequence is the spam avalanche. You sign up for a free webinar from a marketing company. Suddenly, your inbox is flooded with “exclusive offers” from them and their “trusted partners.” That one free app you tried? It’s now selling your email to advertisers. Your primary inbox, once a place for bills and messages from friends, becomes a dumping ground for promotional noise. You waste time sorting, unsubscribing (which often doesn’t work), and deleting. This isn’t just messy; it’s a drain on your productivity and mental peace.
The Data Brokerage Ecosystem
Your email address is a goldmine for data brokers. When you provide it to a website, you’re often agreeing—sometimes buried in a terms of service you didn’t read—to have your data shared or sold. This creates a profile of your interests, location (based on IP), and online behavior. That profile is then sold to other marketers, data analytics firms, and even potentially malicious actors. Your primary email becomes the central thread that ties all these disparate data points together, creating a detailed, monetized picture of your digital life that you have little control over.
The Ripple Effect of a Data Breach
This is the most dangerous consequence. Small and medium-sized websites are frequent targets for hackers because they often have weaker security. When they get breached, the stolen user database is a treasure trove. It typically contains usernames, passwords (often poorly encrypted), and crucially, email addresses. If you used your personal email for that breached site, hackers now have a direct line to you. They can launch targeted phishing attacks (“We detected a login from your bank account, click here…”), try that email/password combination on more critical sites (like your bank or social media), or simply sell your email on the dark web to other criminals. Using a temporary email for low-stakes sites contains this blast radius. A breach only compromises an address that will expire and be reused by someone else within hours.
How Temporary Email Services Work: Simplicity Itself
The magic of a temporary email service lies in its beautiful simplicity. There’s no complex setup, no account creation, and no hidden fees. Here’s the step-by-step process of how it functions as a tool for secure online registrations.

Visual guide about Temporary Email for Secure Online Registrations
Image source: on4t.com
Instant Generation
You visit a provider’s website like Temp-Mail.org, 10MinuteMail.com, or Guerrilla Mail. The site immediately generates a random email address for you, usually something like randomstring123@servicename.com. This address is already active and ready to receive emails. There’s no “Sign Up” button to click. You simply copy the address.
Use It for Registration
You paste this temporary address into the email field of the website you’re registering for. You complete the sign-up, request the verification email, and then switch back to the temporary email tab. Within seconds or minutes, the verification email appears in the inbox displayed on the provider’s site. You click the link, verify your account, and download whatever file you needed.
The Inbox Interface
The provider’s website is your mailbox. It refreshes automatically to show new incoming mail. The interface is typically bare-bones: a list of received emails and a pane to read their content. There are no folders, no labels, no complex filtering. This is by design—it’s a transient tool, not a replacement for your permanent email client.
Auto-Expiry and Recycling
This is the core security feature. The address and all emails in its inbox are automatically deleted after a predetermined time, which can range from 10 minutes to 48 hours depending on the service. Once deleted, that exact email address is recycled and assigned to a completely different user in the future. This ensures no long-term data persistence and makes it impossible for someone to later access emails sent to that address. Your temporary communication history is permanently wiped.
Choosing the Right Temporary Email Provider
Not all temporary email services are created equal. While they all share the same core function, key differences in features, privacy policies, and reliability can impact your experience and security. Here’s what to look for when selecting a provider for your secure online registrations.
Inbox Lifespan and Customization
Check the default lifespan. For most sign-ups, 10-60 minutes is sufficient. For tasks where you might need the email for a few hours (like a delayed support response), a service offering 4-24 hours is better. Some advanced services allow you to choose a custom inbox name (e.g., myname@tempmail.com), which can be easier to remember and type than a random string.
Domain Variety and Reliability
Some websites block known disposable email domains to prevent abuse. If you find your verification email never arrives, it might be because the site’s filter caught the provider’s domain. Using a service that offers multiple receiving domains (e.g., @mailinator.com, @guerrillamail.com, @tmpmail.org) can help you bypass these blocks. A reliable provider will also have high uptime, so your inbox is always accessible when you need it.
Privacy and No-Logs Policy
Read the privacy policy. A reputable service will explicitly state that they do not log your IP address, do not store the emails you receive beyond the display time, and do not sell your data. The entire point is anonymity. If a service requires you to create an account to use a “premium” feature, scrutinize what data they collect. The best services require nothing from you.
Browser Extensions and Mobile Apps
For power users, some providers offer browser extensions (Chrome, Firefox) that generate a temporary email with one click and auto-fill it into web forms. Mobile apps provide the same convenience on your phone. These tools streamline the process, making the habit of using a temporary email for secure online registrations effortless and seamless.
Best Practices for Secure Registrations with Temp Mail
Using a temporary email is a powerful habit, but like any tool, it’s most effective when used correctly. Following these best practices will maximize your privacy and ensure you don’t accidentally lock yourself out of something important.
The Golden Rule: Know When to Use It (and When Not To)
This is the most critical practice. Always use a temporary email for:
- One-time downloads (e-books, whitepapers, software trials).
- Signing up for forums, comment sections, or news sites you visit rarely.
- Accessing free Wi-Fi portals that require an email.
- Registering for online contests or giveaways.
- Trying out a new SaaS tool with a free trial you’re just testing.
NEVER use a temporary email for:
- Any financial service (banking, PayPal, cryptocurrency exchanges).
- Your primary social media accounts (Facebook, Twitter, Instagram).
- Essential cloud storage or password managers.
- Primary email accounts themselves (you need a real recovery email).
- Any service where account recovery or long-term access is absolutely critical.
Forgetting this rule is the fastest way to lose access to something important.
Secure the Temporary Inbox Itself
While the address is public and anyone with the URL can view the inbox, you should still take basic precautions. Do not use a temporary email to send sensitive personal information to others. The inbox is accessible via a simple URL; if you close the tab and lose that URL, you lose access. Copy the inbox URL to a secure note if you anticipate needing it later within its lifespan. Also, be aware that the content of emails is not encrypted by the provider; it’s plain text. Don’t send passwords or confidential documents through it.
Use a Password Manager for the Associated Account
Here’s a pro tip: when you sign up for a site using a temporary email, use a strong, unique password generated by your password manager. This way, even if the site is breached and your temporary email is useless to hackers, the password they get is unique to that site and cannot be used to access your other accounts. The temporary email protects your identity, and the unique password protects the account itself. This is a one-two punch for security.
Check Expiry Times and Plan Accordingly
Before you start a process that might take time (like a multi-step account setup), note the expiry time of your temporary inbox. If you have 10 minutes, don’t start a verification process that might take 30. If you need more time, choose a provider with a longer lifespan. Some services allow you to extend the inbox time with a click—use this feature wisely if available.
The Future of Digital Privacy and the Role of Disposable Addresses
The use of temporary email for secure online registrations is not a fringe tactic; it’s becoming a mainstream component of digital literacy. As data privacy regulations like GDPR and CCPA give users more rights, the tools to exercise those rights are becoming essential. We are moving towards a paradigm of “data minimalism”—only giving companies the absolute minimum information necessary to perform a function.
Integration with Browser Privacy Features
We are already seeing this with built-in browser features. Apple’s “Hide My Email” in iCloud+ and Firefox’s “Relay” service are essentially sophisticated, integrated temporary email systems. They generate unique, forwardable email aliases that can be disabled at any time. This signals a industry-wide acknowledgment that the practice of sharing your primary email everywhere is outdated and risky. Third-party temporary email services are the free, open-web equivalent of these premium features.
Awareness and Behavioral Shift
The future will see a broader shift in user behavior. Just as we now routinely use password managers and two-factor authentication, routinely using a disposable address for non-essential sign-ups will become second nature. Educational campaigns about digital footprints will highlight the email address as the primary tracking key. As more people adopt this habit, the value of a single, shared email address for mass marketing will diminish, potentially raising the baseline of online privacy for everyone.
Limitations and Ongoing Challenges
The battle is not won. Some websites aggressively block disposable email domains, forcing users to either provide a real email or abandon the sign-up. This is an anti-privacy tactic. Furthermore, the temporary email landscape itself has bad actors—some shady providers might log IPs or inject ads. The future will require users to be discerning about which services they trust. The ideal is a decentralized, user-controlled identity system (like those based on blockchain or verifiable credentials) that makes the very concept of an “email for registration” obsolete, but we are likely decades from that being ubiquitous. Until then, the temporary email remains our most accessible and effective shield.
Conclusion: Reclaim Your Inbox and Your Privacy
Your email address is more than a communication tool; it’s the master key to your digital identity. Every time you recklessly share it, you hand a piece of that key to a stranger. The consequences range from the annoying (spam) to the severe (targeted fraud, identity theft). Adopting the simple habit of using a temporary email for secure online registrations is a powerful act of self-defense. It’s a low-effort, high-reward strategy that cleans your inbox, confuses data brokers, and contains the damage of inevitable data breaches.
Start today. Bookmark one or two reputable temporary email providers. Make it a reflex—the moment a website asks for an email that isn’t critical, reach for your disposable address. Combine this with a unique password from your manager. You will immediately notice the difference: a cleaner primary inbox, less promotional noise, and the profound peace of mind that comes from knowing your digital home address is not listed in countless public data broker directories. In the ongoing battle for online privacy, the temporary email is a weapon everyone can wield. Use it.
Frequently Asked Questions
Is using a temporary email legal and safe?
Yes, using a temporary email is completely legal and a safe practice for protecting your privacy. The safety comes from using it correctly—never for critical accounts—and choosing a reputable provider that doesn’t log your activity. It simply creates a buffer between you and the websites you interact with.
Can I receive attachments with a temporary email?
Most temporary email services allow you to receive attachments, but there are often size limits (e.g., 10-25 MB). The attachment will appear as a download link in the email body. Be cautious with unexpected attachments, as with any email, and scan files with antivirus software before opening.
What happens if I need to reset a password for an account I signed up with a temporary email?
This is the primary risk and why the golden rule exists. If you use a temporary email for an account where you might need password recovery, you will be locked out permanently once the inbox expires. You must use a permanent, accessible email for any account where recovery is important.
Do websites know I’m using a temporary email?
Yes, they can often tell because the email domain (like @10minutemail.com) is publicly known as disposable. Some sites block these domains during sign-up to prevent spam and fraud. This is why having a service with multiple domain options can be helpful.
Are temporary emails truly anonymous?
They offer a high degree of anonymity for the recipient. The service provider generally does not know your identity if you don’t provide it. However, the website you sign up with still has your temporary email on record. For true anonymity, you would also need to use a VPN and avoid logging into any personal accounts on the same browser/IP while using the temp mail.
Can I send emails from a temporary address?
Most free temporary email services are receive-only. Their primary function is to let you *get* a verification link, not to *send* emails. Some advanced or paid services offer sending capabilities, but for the purpose of secure online registrations, receiving is all you need.
Leave a Reply